Understanding Malware
This article is several years old. Relative date-based references may be inaccurate.
This article goes into a fairly lengthy but still accessible discussion of Malware: Types of Malware and what they do, how infection spreads, and some preventions.
Types of Malware
Malware is any software that is deliberately harmful to a system or its data. The term could also apply to any software that's not necessarily harmful, but is installed without your permission or knowledge.
Here's some examples.
- Malware that encrypts your files and demands a ransom *1
- Malware that silently enrolls your computer into a "botnet", using it to send spam or attack other systems *1
- Malware that silently exfiltrates (steals) data and sends it to the threat actor's server *1
- Fake FBI warnings indicating your computer was engaged in illegal activity and that you must pay a fine *2
- Fake virus warnings that try to trick you into sending payment for bogus clean-up programs *2
- Annoying advertising, sometimes with random audio, even if you aren't using your web browser at the moment. *3
*1: The most dangerous and destructive, compromising your data and/or attacking other systems
*2: Mostly designed to scare you, not necessarily destructive
*3: Not designed to be harmful, but could be harmful due to poor programming. Certainly it's annoying and unwelcome.
More Details Below on the types of malware outlined above.
Ransomware
The latest class of malware is ransomware. This type of malware is very destructive, encrypting your data then demanding a ransom due within a few days. Amount demanded could be in the low hundreds of dollars and rise dramatically (5, 6, and 7 figures) if the attacker believes you are a large company or government entity. Ransomware is the fastest growing segment of the malware landscape. Early examples include CryptoLocker and CryptoWall. More recent examples include the far-more-virulent WannaCry malware. It's aptly named, too, cause yer gonna wanna cry.
Decrypting the hijacked files on your own or even calling for professional help is generally hopeless because the encryption is industrial strength. Not even professional security analysts can undo the damage caused by most modern ransomware.
Hopefully you have a backup! Paying the crooks, which is never recommended, gives no guarantee of recovering your data. And even if you wanted to pay the ransom, the payment process is quite complex involving irreversible and essentially anonymous Bitcoin. It's unlikely you could research, setup, and fund a Bitcoin wallet in time to make payment.
Click here to read more about encrypting malware.

Cryptolocker ransom screen
Botnet
A botnet, or robotic network, is a large scattered collection of computers (or crappy IoT devices) that obey the commands (issued over the internet) by the threat actor, a "botmaster", who controls the botnet. These infected computers or IoT devices, called zombies, could belong to anyone: home users, companies, government offices, universities, etc.
The users of these computers don't know they're infected as their computers and devices generally continue working as before. This type of malware isn't intended to show itself to- or elicit a response from- the infected user, but rather to attack other systems on the internet or to send spam.
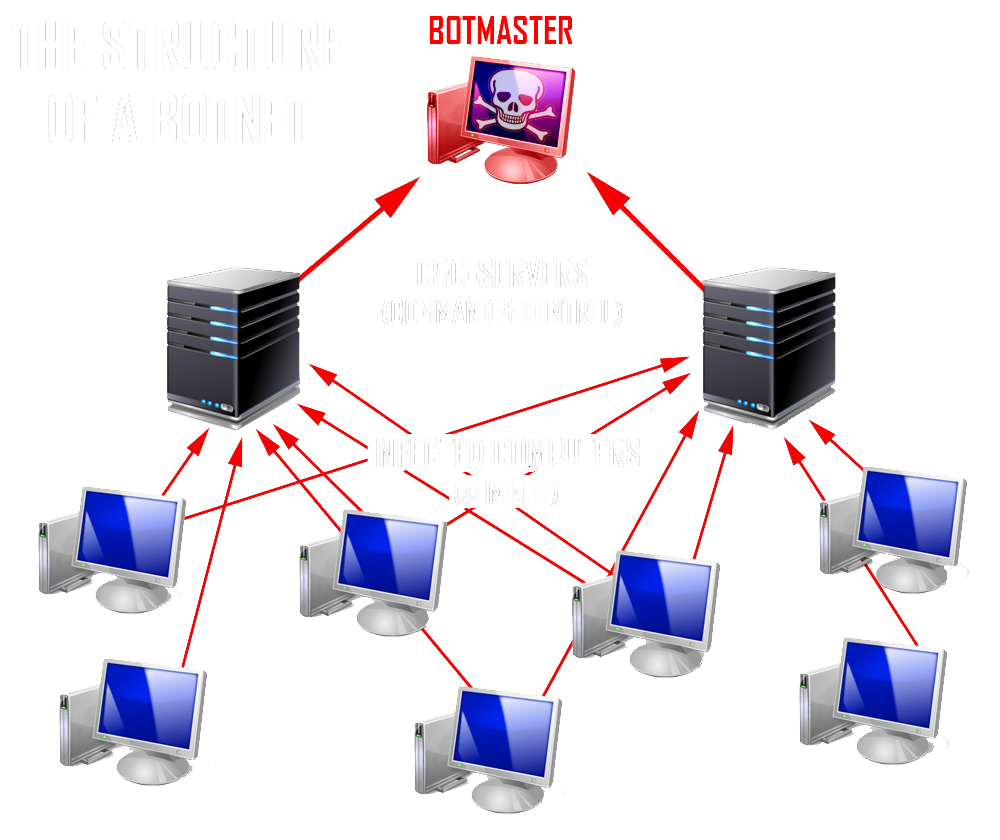
Botnet block diagram
Imagine the computing power that a botmaster could muster if he controlled several thousand or even several million computers and IoT devices scattered about the internet. The botmaster could threaten to attack a company's web servers if they do not pay protection money. This is known as a "DDoS" or Distributed Denial of Service attack.
Or the botnet might be ordered to send millions of spam emails on behalf of a paying customer. This is, in fact, how much spam is sent. In these scenarios, your computer would be part of a marching army without your knowledge! Botnet malware is designed not to hog too much of your computer's resources or cause other damage so you're unlikely to ever notice it's there.
Exfiltration
Sometimes malware is designed to search a company's network for sensitive information that it can steal. For a larger company that might be corporate trade secrets or financial info to assist with trading (using insider information). But for any sized company, large or small, that can include sensitive client information. Don't think that data breaches are limited to Target, Home Depot, Adobe, and other huge companies. Data exfiltration malware could hit anyone.
Losing control of sensitive client information is probably the worst thing that could happen to you and your company. The liability is nearly limitless and it's professionally embarrassing as well.

EXFIL inspired by the EU exit sign
Fake FBI Warnings
These have been around for a while. A full screen with the FBI shield (or some other recognizable law enforcement agency) displays a dire warning about how your computer was used to surf child porn or some other illegal activity. It may say that you must pay a fine or face arrest.
Of course, it's a fraud and you should not pay. Although this malware is usually harmless (it doesn't try to damage your files or computer), getting rid of it can be difficult.
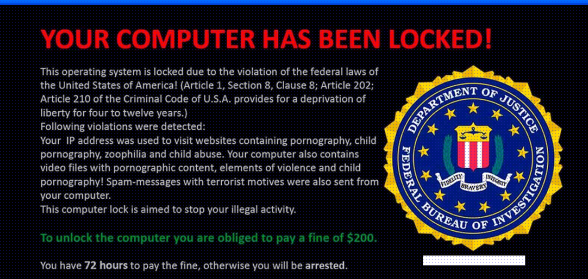
Fake FBI Warning
Fake Virus Warnings
This malware is a fake anti-virus scanner that warns you that your computer is full of viruses. And that if you pay for the "pro" version or make a phone call, it will clean up your computer. Like the fake FBI virus discussed above, this one is usually harmless, but again, difficult to get rid of.
The warning message could be entirely different than the example shown here. But they usually share common themes of dire wording or a phone number.

Fake infection warning
Annoying Adware
This is the least harmful malware -- the "24x7 Help" icon, or other bogus help, that appears on every window.
This really isn't considered malware except that it installs without your explicit permission or knowledge, usually as a hitchhiker with some other product that you did knowingly install. While not necessarily harmful, it's certainly not helpful, either. Fortunately, removal is pretty easy.

24x7 help adware
How Malware Spreads
Infection can spread lots of ways. Here's the most common transmission vectors for infection.
Email: User clicks on links or downloads and opens an infected attachment in a fraudulent email.
Phishing Email: Essentially the same thing except the message is specifically targeting a particular user or occupation. e.g. A administrative assistant may receive an email masquerading as his/her boss. Or a patient may receive an email that appears to be from his/her doctor or vise-versa.
Pirating: Malware is sometimes included in pirated software. There is plenty of pirated software that doesn't include malware, but how can you tell? Unless you are expert at examining pirated software then you'd never know. Don't pirate software.
Drive-by Download from infected website: Visiting an infected web site may automatically download malware to your computer. Fraudulent email often contains links to such infected websites, sometimes with names that look nearly identical to well-known legitimate web sites.
Drive-by Download from infected advertising: Most web sites that display advertising don't host the ads themselves. They are paid by ad-serving companies to include the ads on the web site you are visiting. Ad serving companies don't usually vet the advertisers or check the ads they are pushing to their customer's web sites. This is how your computer can become infected by visiting an otherwise legitimate, uninfected web site. In these cases, the web site itself (that you visited) is clean, but the ads being pushed to it by the ad servers may be infected. Yet another reason to use ad blockers, which are covered in more detail below.
Threat actors are constantly tweaking their delivery and developing new transmission vectors. Some of them are pretty convincing even to the trained eye of a security or I.T. pro. If I.T. geeks like me have to pause for a closer look then what hope does a regular person have? This is where prevention comes in.
Prevention
Keeping Current
If your computer runs Windows then you should be on Windows 10 or later, period. Thankfully nearly all computers are off XP and Vista. But there's still some Win 7 installations still out there. If you are on Win 7 then, really, it's time to upgrade. These older Windows versions are no longer receiving updates from Microsoft -- not even security updates.
Even when Win 7 was receiving regular updates, it was still far more vulnerable to malware and exploits. Win 10 and later, far less so.
For folks that prefer the Windows 7 style start menu (like me), and not the obtuse tiled "Metro" interface, there are ways to make Windows 10 look a bit more like Windows 7. So don't let that dissuade you.
Anti-Malware Security Products
For Windows 10 and later, the built-in Windows Security product is sufficient for most casual users. But for advanced users who tend to download software from less-than-reputable places, visit a lot of web sites, and want a bit of extra protection then I recommend Malwarebytes Premium.
Ad Blockers
No one likes being bombarded with ads so many people use ad-blockers to tamp down the visual noise. Ad-blockers also reduce your odds of becoming infected with malware. Ads containing malware, called malvertising, is a thing so by blocking ads, you reduce the risk of becoming infected from malware-laden ad servers.
A must-have ad blocker and privacy enhancer is uBlock Origin -- an add-on available for all major web browsers.
I understand that many websites survive only because of the ads they serve. But the more obnoxious and frequent the ad, the more money the website makes. It's an attractive offer to the website operator to veer ever closer to the dark side. I have no sympathy for the operators of such sites. It may suck for responsible site operators, but my focus here is protecting users and my clients. Not the income stream to web site operators. If enough people block ads then perhaps ad server companies will tone it down a bit and vet their advertisers more carefully. One can hope, right?
Sandboxing Your Browser
Sandboxing is a computing term that means to trap or contain a process (like a program or a web page) within a virtual container to prevent it from affecting (harming) things outside of the container. A sandbox "looks like" the host computer and will accept and react expectantly to damaging commands from a hostile program, but in reality won't allow those commands to exit the sandbox.
For instance, if a sandboxed virus tries to infect your computer, the sandbox (looking like the entire computer) will react as though the virus succeeded. But in reality the infection is limited to the sandbox. Initializing (resetting) the sandbox in the event of infection is quite simple. Nothing in this world is perfect, but sandboxing programs do a pretty good job of containing viruses.
Using a sandboxing product, like Sandboxie, does require some understanding and savvy on the part of the user, especially where downloading legitimate files is concerned. These concepts are easy to understand but they must be discussed and learned. I can help with that!
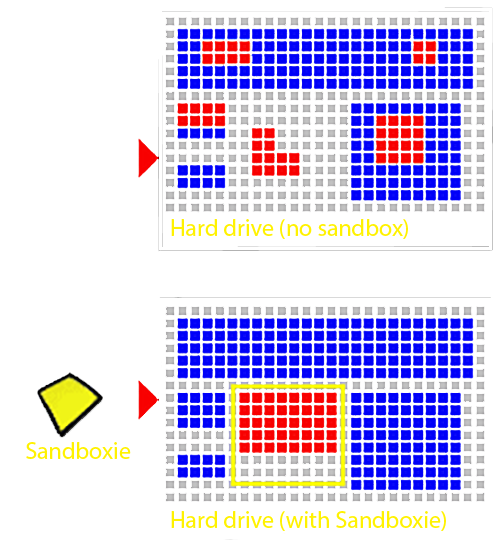
Sandboxie how it works diagram